Model repute has the capability to alter faster than ever earlier than, and in 2026, there are extra potential dangers than ever earlier than. Model security has historically been relegated to defending manufacturers from promoting on or close to inappropriate content material on-line, however it additionally now has to embody monitoring your natural content material and what persons are saying about your model on social, and scoping out different safety threats.
The place as soon as there have been a restricted variety of information sources to watch, this has ballooned and fragmented. There are actually six networks the place shoppers get information a minimum of as soon as per week, and extra conversations to concentrate on than ever earlier than throughout platforms. There are decentralized communities, content material automation and platform rule volatility, plus the brand new menace of generative AI creating virtually something on the click on of a button.
Preserve studying for actionable methods you should use model security instruments and examples of efficient ones that may assist you decrease threat on social.
What are model security instruments?
Model security instruments have been historically automated options that protected your model from threats on social media and different digital channels like your adverts showing alongside distasteful content material. Nonetheless, this definition has broadened to incorporate instruments that monitor on-line conversations, guarantee brand-safe partnerships and acknowledge the place potential threats exist that would negatively affect your model.
With this intel available, you’re empowered to reply to reputational dangers earlier than they grow to be a full-blown disaster, and develop the breadth of your company communications technique.
6 key methods to make use of model security instruments to guard your repute
From promoting safeguards to real-time threat detection, listed below are 5 methods you should use model security instruments to guard your model’s repute on-line.
Platform-level management and promoting safeguards
Your first line of protection in opposition to your branded adverts showing alongside offensive content material contains the in-platform instruments that main social networks have. Issue them into your social media promoting technique to reduce threat and maximize the affect of your campaigns.
Meta platforms: Meta affords a number of model security controls that work throughout Fb, Instagram and Messenger. These options will let you select the extent of management over the place your advert seems. Placements might be restricted by content material matter, format and supply.
X: X’s model security instruments supply each technical and normal recommendation on how you can hold your model protected on the community. These options will let you hold X a protected place on your model and neighborhood by providing key phrase blocking and sensitivity settings, amongst different controls.
YouTube: YouTube’s model security options are according to these obtainable via Google search and show adverts.
TikTok: TikTok launched its Model Security Heart to supply entrepreneurs with up-to-date information and proposals on model suitability throughout the community.
These network-provided security instruments assist cease model commercials from showing subsequent to delicate content material, however it’s not all about paid any extra.
Social Listening for real-time threat detection
To guard your model’s repute, it’s necessary to concentrate on the complete image with regards to dialog round your model. This goes far past feedback that point out your model immediately or in your owned posts, and extends into the broader ecosystem inside which your model exists.
For instance, should you’re a shopper packaged items (CPG) model, you’ll need to concentrate on conversations about your model, whether or not it’s about inflation or a narrower matter corresponding to packaging sustainability. It’s essential to watch all of those adjoining matters as manufacturers might be introduced into these conversations, so understanding how that ecosystem works and any growing narratives is essential.
Sprout Listening can present you key metrics with regards to detecting dangers. For instance, observe off-brand hashtags to see the place threat emerges, or have a subject monitoring seek for one of many eventualities above to see if there’s any message spike in matters related to your model.
If there are, you’ll be able to then use sentiment evaluation to find what persons are saying about any given incident, and whether or not that dialog is constructive or adverse so that you’re armed with context when deciding to reply.
Along with this evaluation, NewsWhip by Sprout Social supplies a layer of predictive intelligence on media protection and social posts, figuring out the narratives which are rising throughout the social net to allow your staff to make knowledgeable selections about response rapidly.
With real-time threat detection applied, escalations and responses occur sooner, defending your model fairness from exterior threats.
Message monitoring and disaster triggers
Dashboard-level evaluation is beneficial, however realistically, it’s not possible to watch a dashboard all day, every single day. That’s why automation must be an important a part of model security.
Social inboxes are a extra direct sign for measuring model well being. For essentially the most half, a median quantity of messages means issues are enterprise as traditional. However an sudden spike might be trigger for concern. It may point out a PR catastrophe is on the horizon or has already arrived. To watch this, you should use instruments corresponding to Message Spike Alert notifications related to Sprout’s Sensible Inbox. When incoming messages throughout your social platforms exceed the hourly common, you instantly get electronic mail or cellular push notifications. Plus, you’ll be able to customise the software’s sensitivity settings to make sure the protocol is acceptable on your staff.
Knowledge safety & regulatory compliance
Some model dangers stray into authorized territory. For manufacturers working in regulated industries, corresponding to healthcare or finance, there are strict guidelines with regards to knowledge privateness and the data that’s placed on social media.
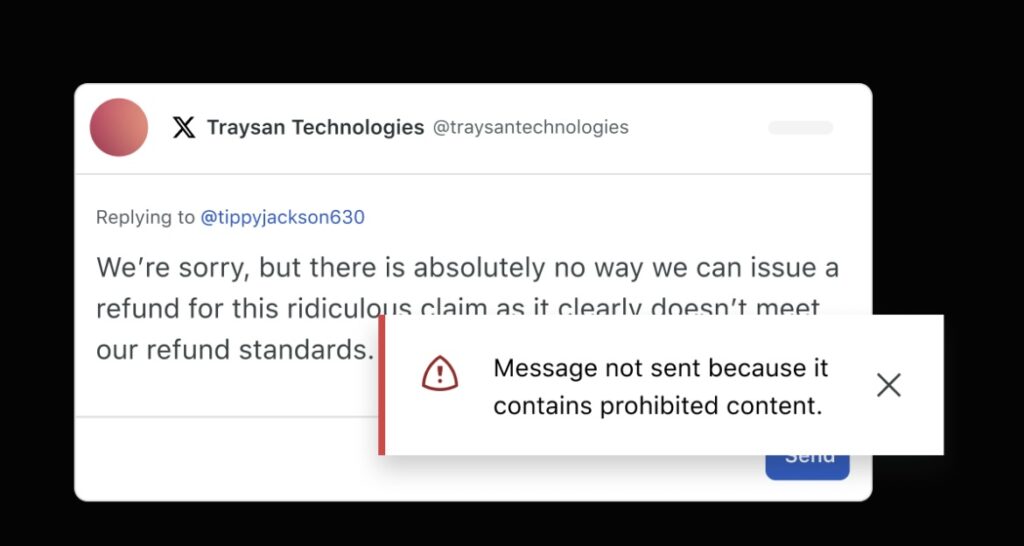
Instruments corresponding to Guardian by Sprout Social add an additional layer of safety on high of your regular efforts should you work in a regulated business. Guardian lets you management each enter and output, together with masking delicate knowledge robotically, securing varieties and blocking key phrases.
This offers you the power to have interaction successfully whereas making certain compliance, defending delicate knowledge and sustaining model integrity. This helps you keep belief together with your prospects by demonstrating a dedication to their safety.
Influencer and creator security options
Influencers are the brand new face of promoting for a lot of manufacturers, with the authenticity and dependable audiences they create confirmed to be a precious dovetail with extra conventional advertising and marketing strategies. In response to our 2026 Social Media Content material Technique Report, creator content material is the third-most cited content material that entrepreneurs plan to prioritize in 2026.
However with that authenticity comes threat. They don’t seem to be your model’s staff—that’s a part of the worth. They’ve their very own audiences, a historical past of on-line feedback and values of their very own.
Earlier than working with influencers and creators, it’s essential to vet them, weigh up the dangers and construct customizable security studies that assist you align creators together with your model’s values. For instance, Sprout Social Influencer Advertising and marketing robotically scans a creator’s previous content material for “crimson flags” like grownup content material, playing or political controversy.
When you make sure that any influencers you’re employed with are model protected, you’re lowering the chance your model shall be pulled into any unsavory conversations or conditions began by individuals outdoors of your group.
Worker advocacy and inner security gates
When staff share model content material, they amplify your attain and offer you a strong endorsement. Nonetheless, even essentially the most well-meaning staff can tip public favor in opposition to you by saying the incorrect factor, and even simply saying the appropriate factor on the incorrect time.
With worker advocacy, you’ll be able to present your staff with pre-approved social messages to share. These assist preserve a constant model voice and allow your staff to simply and confidently comply together with your model pointers. You’re additionally capable of limit the obtainable social networks your content material might be shared on,reducing your threat of legal responsibility even additional.
Greatest model security instruments to think about
Listed below are a number of the finest instruments for managing model security that you just may need to think about when planning out your technique.
Sprout Social
Sprout Social affords a set of AI-powered options for social media administration and media monitoring that assist you shield your model. Our platform improves your model security on social with voice of the shopper knowledge, and automatic instruments and processes, together with:
Publishing and compliance
Sprout’s messaging and approval workflows make sure that no content material goes dwell with out approval. This may embody evaluations by managers to any submit that’s set dwell, evaluations by authorized groups via a safe hyperlink (even when they don’t have a Sprout Social account) and added protections for regulated industries via Guardian.
You can even construct a repository of pre-approved property to make sure that every part posted on social media is brand-appropriate and vetted.
Monitoring & disaster administration (proactive safety)
Sprout Listening and NewsWhip by Sprout Social give groups a way of the broader panorama past mentions and messages. With Listening, you’ll be able to monitor sentiment and spikes in curiosity across the net through key phrases, model hashtags and competitor mentions to gauge notion of any model or concern.
NewsWhip affords media protection monitoring of any matter through agentic AI in addition to social media alerts to maintain observe of how information is spreading on-line. This predictive intelligence places you forward of any rising narrative, and lets you make an knowledgeable resolution on whether or not your model must be reacting to these modifications in media and public curiosity. The Trellis monitoring agent will provide you with a warning on to your inbox if something modifications primarily based in your chosen key phrases, model and sensitivity thresholds.

This aids with institutional consciousness of moments of potential reputational harm. Many disaster groups develop benchmarks of escalation to know what degree of protection and/or social sharing requires an escalation vs. it being one thing that may be dealt with by a smaller staff.
Past agentic monitoring, conventional social alerts additionally serve the same operate so that you can be alerted when a subject is trending.
The Trellis AI Agent additionally runs inside Sprout Listening, which permits customers to interrogate the info immediately throughout the dashboard via the agent for deeper evaluation of the explanation behind modifications within the dashboard.
Influencer security
Sprout Social Influencer Advertising and marketing affords quite a few instruments to handle the potential dangers of working with influencers. These embody a model security software that scans a creator’s previous content material for potential points, and customizable security guidelines that use AI to recommend and flag key phrases or hashtags in an influencer’s historical past that don’t align together with your values. There are additionally tolerance thresholds that allow you to set particular ranges for security guidelines (e.g., “flag if greater than three posts point out a competitor”) to steadiness threat with alternative.
Group and evaluation administration
Evaluation websites and boards are one other place the place a disaster can start, as prospects voice their frustrations with adverse experiences. With Sprout’s neighborhood and evaluation administration instruments, you’ll be able to:
Monitor and reply to evaluations on Google My Enterprise, Yelp, Glassdoor, and TripAdvisor from one place to handle adverse suggestions instantly.
See in real-time when one other staff member is viewing or replying to a message, stopping “double-responses” that look unprofessional.
Monitor Reddit conversations about your model or the adjoining business and flag any dangers that emerge.
Proofpoint
Proofpoint is a digital threat safety answer that fortifies manufacturers, knowledge and personnel in opposition to cyber assaults throughout the deep and darkish net. This deep evaluation ensures that your model is protected in areas that you just won’t in any other case assume to look.
You should use it to:
- Uncover model misuse, fraudulent accounts and govt impersonations throughout world social platforms.
- Scan the deep and darkish net for compromised credentials, leaked knowledge and bodily threats.
- Obtain alerts and orchestrate automated takedowns for dangerous accounts, phishing domains and malicious content material.
Zefr
Zefr permits digital promoting effectiveness whereas making certain model suitability and security values are upheld throughout the world’s largest networks.
They concentrate on AI-powered model suitability options that will let you:
- Activate and measure model suitability utilizing pre-impression content material avoidance controls.
- Allow exact promoting activation whereas navigating fashionable, complicated content material dangers, together with misinformation, deepfakes and unregulated AI-generated media.
- Remove misaligned impressions from false positives and unsuitable content material.
ZeroFox
ZeroFox supplies safety that scours the floor, deep and darkish net to establish and dismantle exterior threats to your model identification and personnel.
You should use it to:
- Determine and orchestrate the takedown of pretend govt profiles and model impersonators.
- Detect phishing campaigns and spoofed domains designed to steal buyer credentials.
- Monitor the darkish net for leaked firm knowledge, compromised credentials or focused chatter.
Greatest practices for integrating model security instruments into staff workflows
There are loads of methods to arrange profitable model security administration. Beneath are key steps that guarantee it’s embedded within the tradition of your group slightly than an afterthought.
1. Set up clear possession and escalation paths
There are a number of facets to model security, from adverts to content material publication to influencer administration, and every workflow might need totally different possession. That’s why there have to be clear possession and a disaster plan if one thing does go incorrect, whether or not that’s looping within the comms staff or sending flags to stakeholders.
2. Embed security checkpoints into content material approval workflows
There ought to by no means be a single level of failure for content material publication, which is why it’s necessary to have approval workflows. Use instruments to let managers have closing sign-off on posts earlier than they go dwell to ensure model security is entrance of thoughts. That is significantly true in regulated industries, the place you may need to arrange an inventory of banned phrases to make sure compliance.
3. Automate alerts and threshold triggers
No one has time to watch a dashboard all day, which is the place alerts are available. Be sure you’ve arrange automated alerts to let you already know when issues change, whether or not that’s message quantity, media protection or model mentions.
4. Align security standards throughout paid and natural groups
Paid and natural groups have to be working from the identical standards, so guarantee that everybody throughout each groups is conscious of security pointers, banned phrases and escalation protocols.
5. Standardize influencer and accomplice vetting processes
Nonetheless you select to vet the influencers you’re working with, it’s essential the method is constant. Develop standards and model values that require alignment and stick with them.
6. Doc response playbooks and SLAs
Essentially the most mature groups have disaster response playbooks and escalation guides that doc every part wanted to reply successfully to crises or potential crises. Be sure you have one too.
7. Combine security metrics into efficiency dashboards
Don’t hold model security in a silo, it’s one thing that impacts everybody. Be certain that security metrics (whether or not that’s advert adjacency, a discount in disaster escalations or adverse information tales) are reported alongside different efficiency indicators.
8. Conduct common audits and post-incident evaluations
Simply because it’s good to have a plan in place in case a disaster does strike, you must all the time pay attention to previous efficiency to enhance future efficiency. When you do have an incident, return and analyze the place it began, what went incorrect and the way your staff may have responded otherwise.
9. Practice groups constantly
The web is all the time evolving. Be certain that your staff is conscious of all the brand new options in your software stack.
10. Reassess threat as platforms and tradition evolve
This final level applies to the enterprise too. New dangers will emerge as expertise and on-line tradition proceed to evolve. Your enterprise must have the instruments obtainable to handle this new actuality.
Measuring success
Model security self-evidently has worth, and like all issues that drive worth for a enterprise, it’s necessary to measure how the groups concerned are contributing to that worth.
It will rely in your group’s priorities and whether or not your focus is on natural, paid or earned media, however success typically entails some or the entire following:
- Declining variety of unsafe advert placements
- Much less time to establish a brewing disaster
- Discount in disaster escalations attributable to early motion
- Fewer adverse information tales
- Higher sentiment round campaigns
- Benchmarking the affect of brand name security instruments
- Integration of security metrics into govt dashboards
Nonetheless you determine to measure it, hold it constant and common, with ties again to enterprise affect to display the significance of the work to the broader staff.
Model security in 2026 and past
Incorporating model security options into your workflow will strengthen your model and forestall reputational dangers from morphing into severe enterprise harm. Nevertheless it’s now not sufficient to be reactive when one thing goes incorrect.
Just like the web, the dangers to your model might be exponential, whether or not that’s an advert showing subsequent to an offensive submit, adverse media protection or an influencer going in opposition to model values. The proactive administration and reporting on these dangers are the one method for a model to actually keep protected on-line.
Begin assessing your model security measures and take actionable steps to enhance it with our model security guidelines.



